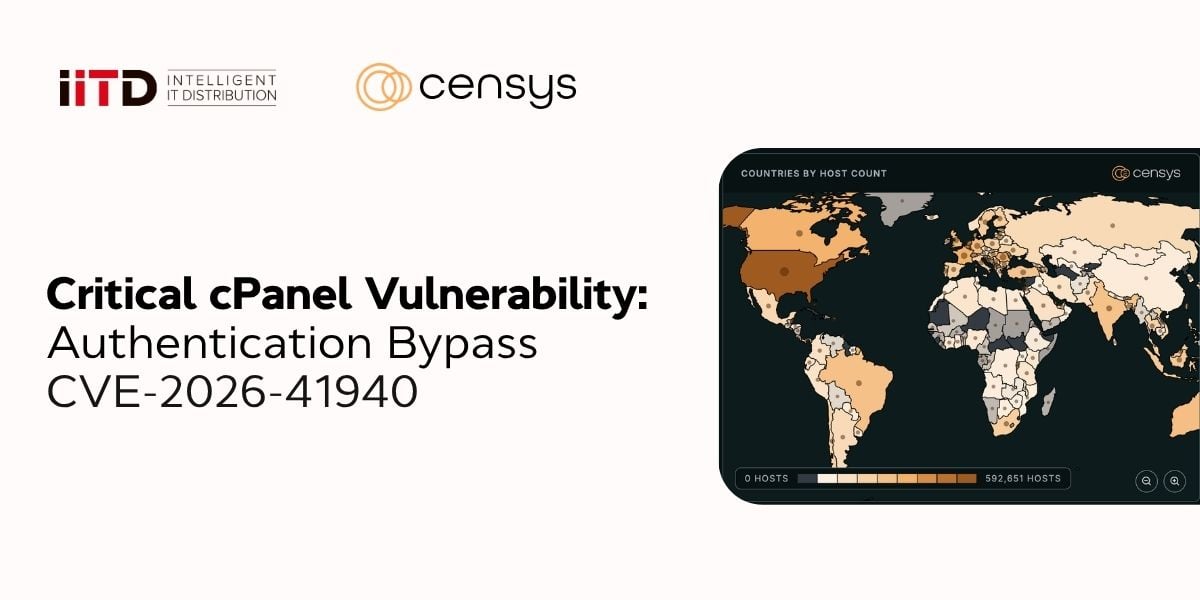
Critical cPanel Vulnerability: CVE-2026-41940 Authentication Bypass
At the end of April 2026, corporate infrastructure faced a large-scale threat — experts detected a critical vulnerability CVE-2026-41940 with a maximum rating CVSS 9.8 in popular control panels cPanel and WHM. According to the analytical platform Censys, the global attack surface encompasses about 1.1 million exposed hosts and 6.7 million web properties. The flaw allows a remote unauthorized cyber attacker to gain full administrative access to the server without credentials entry. This necessitates the immediate implementation of containment protocols by IT teams.