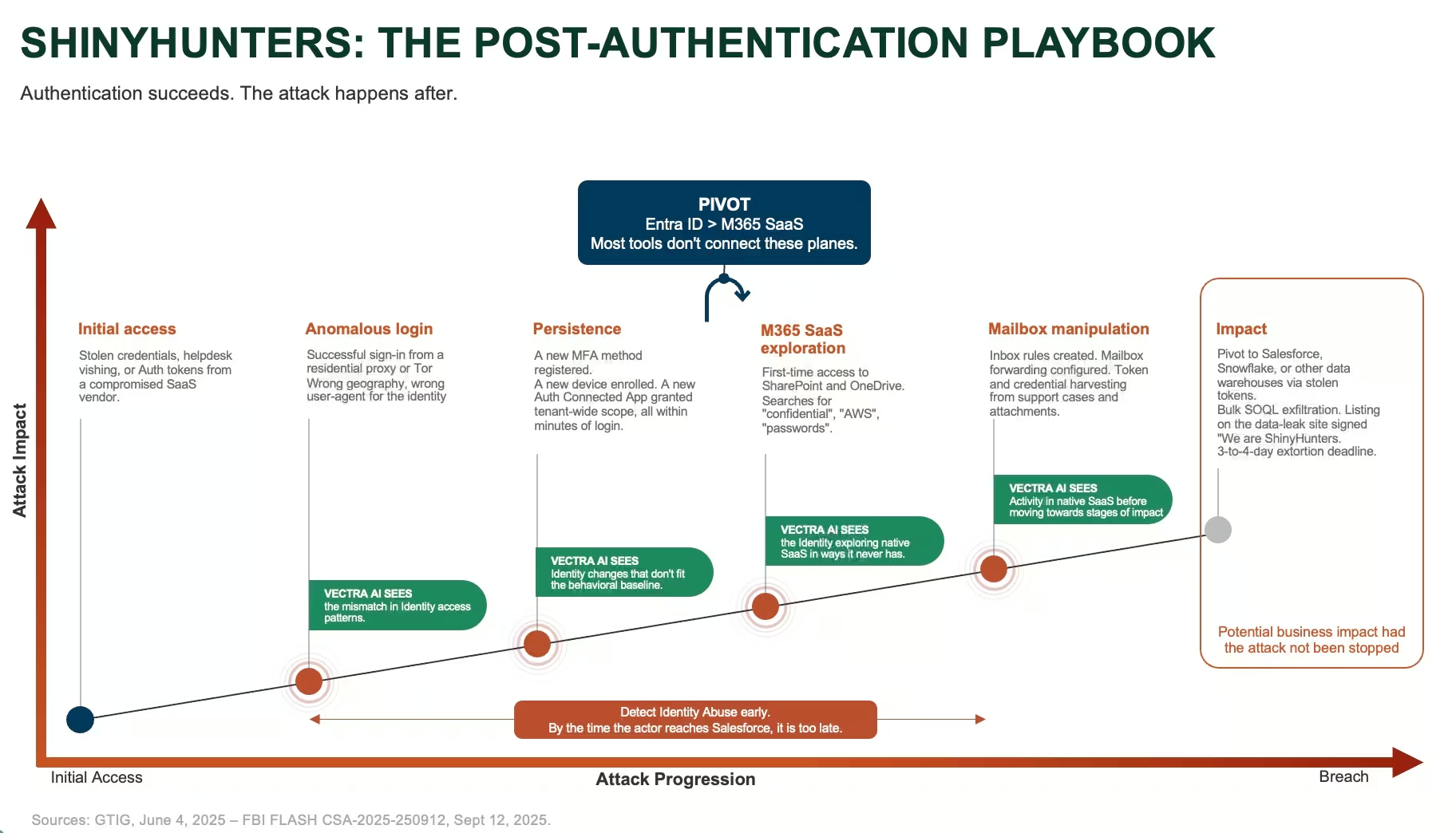
Baseline cyber hygiene recommendations remain essential, but modern attacks are engineered specifically to bypass those barriers. Vectra AI emphasizes that traditional detection tools have not lost their effectiveness — they are simply incomplete, because they focus exclusively on events that occur before successful authentication. Modern architectures built on the Zero Trust model require continuous oversight to determine whether current activity aligns with the user’s established profile.
Specialized solutions from Vectra AI make it possible to detect threat actor activity after successful login, operating in the blind spot left behind by classic security controls. Cross-platform analytics automatically correlates data across different environments, transforming fragmented allowed events into a clear chain of suspicious activity. That enables security teams to isolate threats quickly, before critical data exfiltration begins.
In summary, focusing on specific groups or isolated indicators is a conceptual mistake. The strategic value of modern defense lies in changing the trust model: successful authentication no longer guarantees operational security. The true line of defense is the ability to detect behavioral anomalies in real time.
iIT Distribution is an official distributor of Vectra AI solutions and provides partners and customers with expert support at every stage of security project delivery. The iITD team helps select the right tools for behavioral analytics, designs solution architectures aligned with the Zero Trust model, and conducts resilience assessments of enterprise SaaS environments. The company’s specialists serve as a trusted extension of the partner team, delivering high-level guidance from initial needs assessment through full-scale implementation of cyber threat defense systems.